Two-factor authentication (2FA) is a security mechanism that requires users to provide two different forms of identity authentication when accessing digital systems or services. These two factors typically involve something the user knows (e.g., a password) and something the user has (e.g., a mobile phone or token). Combining these two factors increases the security of access and minimises the risk of unauthorised access.
In a digital environment where rapid technological advances are taking place, security is a key factor for protecting sensitive data and information. Two-factor authentication provides an effective means of preventing unauthorised access and protecting against potential security threats such as identity theft, phishing and account attacks. It is essential for both users and organizations that value the security of their digital activities and accounts and internet safety.
How Does Two-Factor Authentication Work?
Two-factor authentication (2FA) is a security mechanism that requires two different ways to verify a user's identity. This increases the level of protection for digital accounts and information. The basic concept is to combine several authentication factors that a user must successfully pass in order to gain access to a system or service.
Two-factor authentication combines several categories of authentication factors. The first factor is usually something the user knows, such as a password. The second factor is something the user has, such as a physical device or biometric. The combination of these two factors enhances security by ensuring that even if one factor is compromised, further authentication is required.
Forms of two-factor authentication
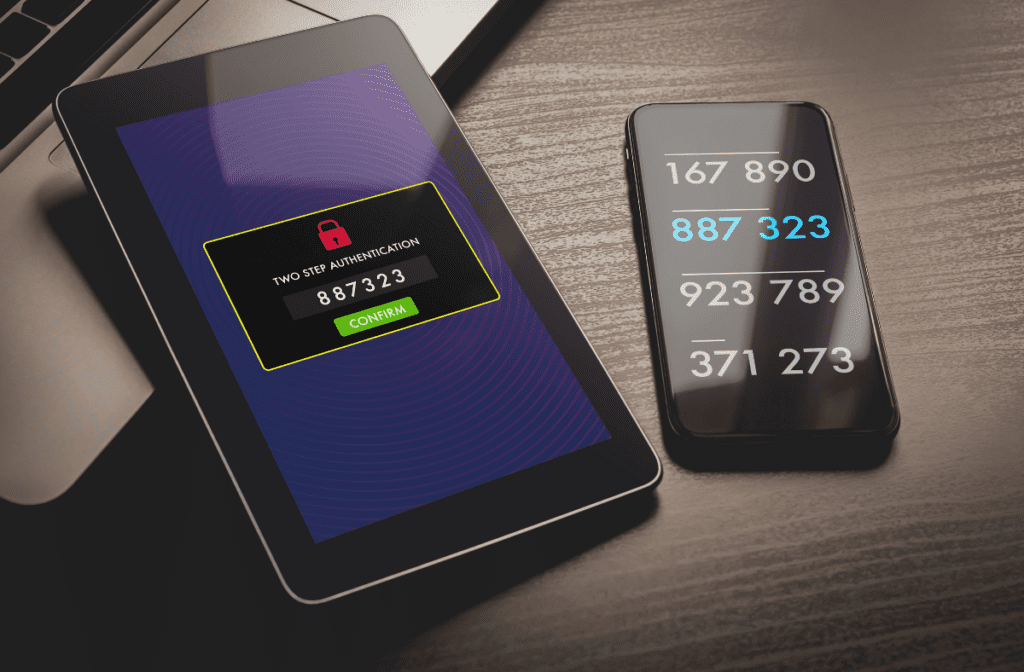
Code sent to mobile phone:
- One of the most common methods of the second authentication factor is to send a one-time code to the user's mobile phone. This code can be obtained via SMS, mobile apps or email.
Hardware tokens:
- Hardware tokens are physical devices that generate or display one-time codes. Users can carry the device with them or use it only for specific logins. This form provides an additional layer of protection.
Biometrics:
- Biometric two-factor authentication uses the physical characteristics of the user, such as fingerprints, facial recognition or eye scans. This data is unique to each user and provides a high level of security.
Code generation applications:
- Users can use mobile apps that generate one-time codes, for example using the TOTP (Time-Based One-Time Password) algorithm. These codes are automatically renewed after a certain amount of time, increasing security.
Reasons for Using Two-Factor Authentication
Two-factor authentication (2FA) is becoming an essential tool in the fight against security threats in the digital environment. Its implementation brings several key benefits:
Increased Security
Password theft protection:
- One of the main benefits of 2FA is the elimination of vulnerabilities associated with using only passwords. Passwords can be easily compromised by phishing, social engineering, or data leakage. 2FA ensures that even if an attacker obtains a password, they will not be able to access it without a second authentication factor.
Resistance to attacks on accounts:
- Attacks on accounts are a common occurrence in the digital world. 2FA increases resistance to these attacks because even if an attacker obtains the password, without the second factor, they will not be able to gain access.
Prevention of Phishing and Malware
Implementing 2FA reduces the risk of successful phishing, where an attacker deceives users into providing sensitive information. The combination of something the user knows (a password) and something the user has (e.g., a code sent to a mobile phone) complicates the attacker's task.
Additional Benefit When Password is Lost:
When passwords are lost, whether due to forgetting or theft, 2FA provides an additional layer of protection. An attacker would need not only the password, but also access to a second factor, making unauthorized access more difficult and increasing the security of digital accounts.
Given the ever-increasing risks associated with cyber threats, two-factor authentication is a key tool for protecting user accounts and sensitive information. It is a security investment that ensures digital identities are effectively protected from modern security challenges.
Risks and Limitations of Two-Factor Authentication
Two-factor authentication (2FA) brings a number of benefits, but it is not flawless and some challenges and limitations need to be considered.
Possible Security Deficiencies
There are potential risks to the implementation of the 2FA that may undermine its effectiveness. For example, if a second authentication factor, such as a mobile phone or hardware token, is lost, the user may have problems accessing their account. Further, some forms of 2FA, such as SMS codes, may be more susceptible to attack if an attacker manages to gain access to the user's mobile number.
User Convenience vs. Safety:
Sometimes it can be a challenge to find a balance between user comfort and safety when using 2FA. Some methods may be considered impractical or unnecessarily complicated by users, which can lead to a reluctance to use this security layer. Proper implementation and educating users on the importance of 2FA can help overcome this challenge.
Technology Challenges and Compatibility:
2FA may encounter technological and compatibility challenges when integrating with different systems and services. Not all digital platforms support the same forms of 2FA, and this can cause problems if a user wants to leverage this layer of security across different applications and systems. There may also be compatibility issues with different types of hardware tokens or biometric systems.
Conclusion
In conclusion, two-factor authentication (2FA) is an important security measure in the digital world. Despite some challenges, such as possible security flaws or limitations in convenience for users, 2FA is essential to protect against cyber threats.